Explore by tag
All Tags
Set it and forget it is no longer enough for Google Workspace security
AI tools like ChatGPT and Claude have made it remarkably easy to connect third-party apps directly...
10 practical ways to secure your Google Workspace in 2026
Google builds a lot of security into Workspace, but they cannot control how your team uses it. If a...
Most popular
Why Zero Trust is the new gold standard (and why it isn’t just an enterprise tool)
The traditional “castle-and-moat” approach to cybersecurity — where we assumed everyone inside the...
Cloud security in 2026 (part 3): Securing generative AI on AWS and Google
We’ve already secured the business strategy and the identity architecture. Now, we face the final...
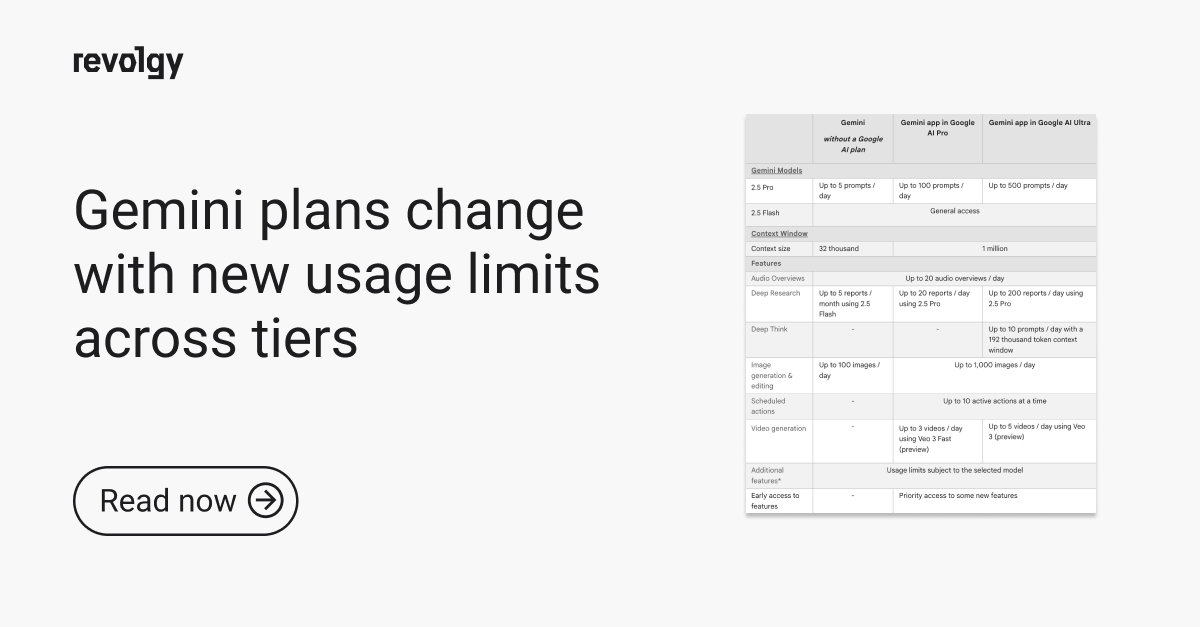
Cloud security in 2026 (part 2): Why identity is your new firewall
Your data now lives on servers you don’t own, it is accessed by employees working in coffee shops,...
Cloud security in 2026 (part 1): From shared responsibility to shared fate
If you are still using a security strategy from 2023, you have a problem. The old idea that the...
Why Google says human security teams won’t be fast enough to stop threats by 2026
We’ve spent the last few years treating AI as a productivity booster. But Google Cloud’s new...


.webp)
.webp)

.webp)